Endpoint protection: how to get inside the hacker's mind to defend your business
Endpoint protection is one of the most critical challenges for any business today. But there is a paradigm shift taking place: it is no longer enough to correct vulnerabilities, we must start thinking like a hacker.
In this article, we explain how to adopt a Strategic and Proactive Approach to Cybersecurity, concretely improving the security of your business.
Why traditional vulnerability management is no longer enough
If you're in IT or security, you've probably already found yourself in this situation: an endless list of Vulnerability to be corrected and the feeling of never being able to keep up.
The problem? The idea of eliminating all vulnerabilities is simply unrealistic. Hackers don't work like that. They are not looking for the perfect flaw, but the one that is easiest, fastest and most effective to exploit. This means that even a small carelessness can turn into a serious attack.
The key point is this: you don't have to protect everything the same way, but understand what's really at risk.
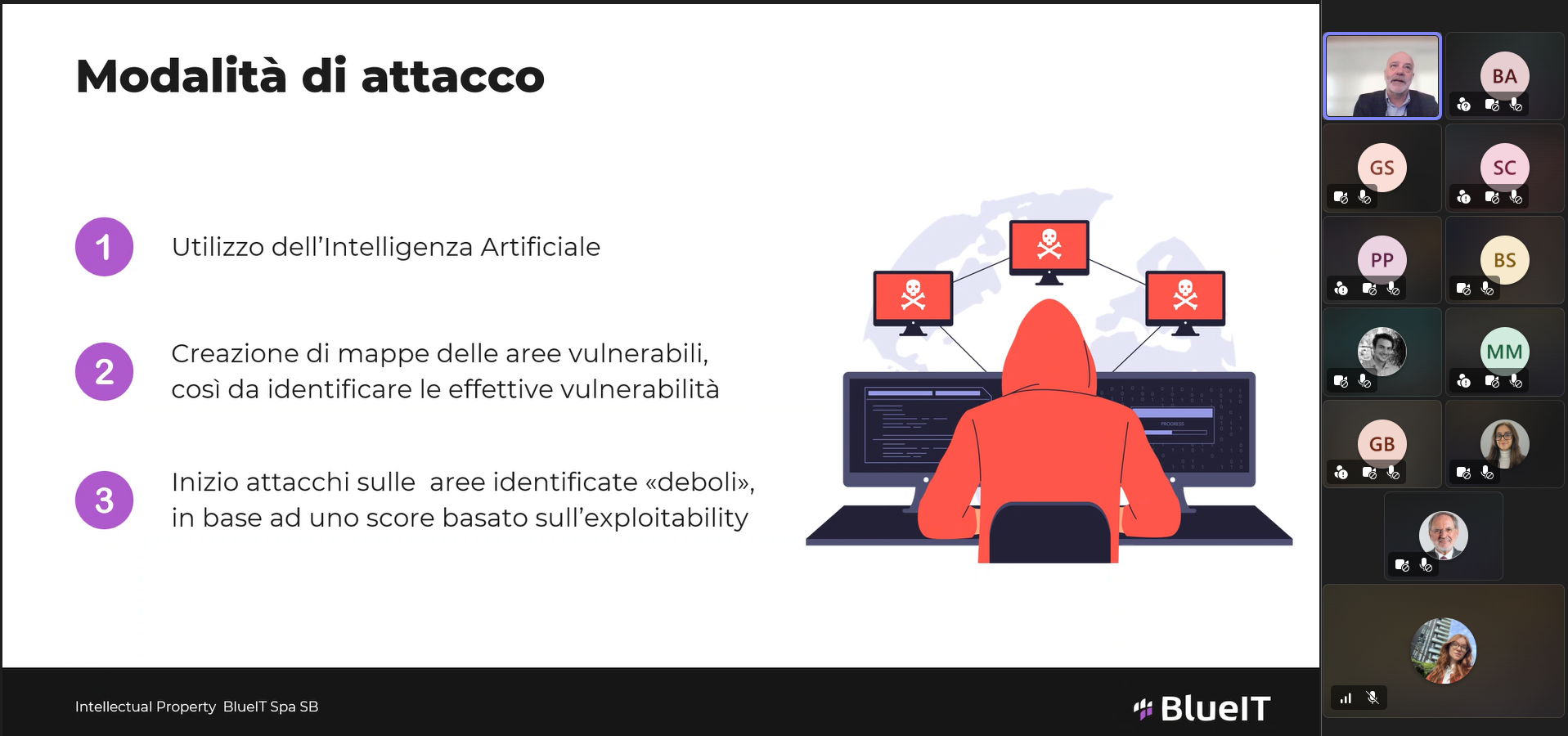
How a hacker thinks: from theory to real attack
Imagine for a moment looking at your company through the eyes of a hacker. He doesn't see firewalls, policies, or procedures, but opportunities.
Start by silently analyzing the attack surface, mapping every endpoint, every access, every possible weak spot.
It is not looking for the perfect vulnerability, but the simplest one, the one that requires the least effort and offers the greatest result.
Once identified, it enters without making a sound and moves sideways, exploring the infrastructure as if it were a territory to conquer.
Today, this process is no longer manual: it is automated, fast, scalable. The time between the discovery of a vulnerability and its exploitation has drastically reduced, turning any delay into a real risk.
From reactive defense to proactive strategy
Now turn the perspective around. What if your company could take the same path, but in advance?
This is where an advanced approach to cybersecurity comes into play: simulating attacks before they happen, understanding the most critical paths and intervening in a targeted manner.
It's no longer a matter of correcting everything, but of seeing everything, prioritizing what really matters, and acting quickly and precisely. It means having full visibility on assets, even hidden ones, evaluating vulnerabilities based on their impact on the business, and combining automation and human control to respond effectively.
In this scenario, so-called critical points emerge: strategic nodes that, if protected, block entire chains of attack. This is where the real security game is played. Not in doing more, but in doing better, transforming Cybersecurity from a necessary cost to a strategic lever for growth and business continuity.
The BlueIT webinar course on cybersecurity continues with the aim of providing concrete tools and strategic vision to face a context of constantly evolving threats.
Use the button below to reserve your spot for the next webinar.
.png)
Ready to strengthen the security of your Endpoints?
Assessing the real risk is the first step in reducing it: after analyzing your attack surface, we identify critical points and define a concrete and measurable action plan.
Contact us for an initial assessment and find out how to transform cybersecurity into a competitive advantage for your company.
.png)
The most popular articles
Discover the latest news and trends


.png)
.png)
