Corporate cybersecurity and NIS2: because the real risk today is the human factor
In the current scenario of corporate cybersecurity, a fundamental principle emerges more and more clearly: cybersecurity does not depend only on technology, but above all on human behavior. Systems such as Firewall, Antivirus and Advanced Protection Solutions they remain essential, but they are no longer sufficient on their own to counter a constantly evolving threat landscape. The real point of exposure, today, is in fact the human factor.
This is because attack techniques such as phishing, vishing (a type of fraud that uses the telephone as a tool to obtain personal data—especially banking or credit card information—and subsequently steal varying amounts of money) and social engineering have evolved significantly thanks to the use of artificial intelligence, becoming extremely realistic. Perfectly constructed emails, credible urgent communications, and synthetic voices that are almost indistinguishable from real ones make it increasingly difficult to recognize an attack.
This shift in risk leads to a key conclusion: human behavior is today the main surface of exposure in cyber attack strategies.
When artificial intelligence amplifies the capacity of attackers
If the human factor represents the point of vulnerability, it is precisely artificial intelligence that has made this risk even more critical. Modern attack techniques are no longer static or easily recognizable, but adaptive and highly automated. In fact, AI allows you to:
- Make phishing campaigns highly personalized and credible
- Generate synthetic voices used in vishing cases
- Automate the collection and use of stolen credentials
- Develop increasingly sophisticated and difficult to detect malware
This level of evolution radically changes the scenario: it is no longer enough to defend yourself with traditional technological tools. Security must be rethought as an integrated system, in which Technology and human behavior work together. In this context, people's awareness becomes the first level of defense, because no technical system can fully compensate for human error exploited by a well-constructed attack.
From risk to active defense: the Human Firewall model
If the problem is human behavior, the answer can only start with the people themselves: this is where the concept of Human Firewall, one of the pillars of modern corporate cybersecurity, comes into play. The idea is to transform every employee from a possible point of vulnerability to an active element of corporate defense: this transition does not take place only through technological tools, but above all through culture, training and awareness. In an effective Human Firewall model, security becomes an integral part of daily business processes: it is no longer a separate activity, but a continuous behavior.
This approach is developed through three closely linked elements:
- Continuous training based on realistic attack scenarios
- Phishing and Vishing Simulations to Strengthen Recognition Capacity
- Constant monitoring of cyber posture and risky behavior
These elements are not isolated, but they work together to build a more resilient security ecosystem, where the organization is able to reduce risk before it even turns into an accident.
NIS2: when safety becomes a measurable and continuous requirement
The transition from theoretical security to truly effective security is made even more evident by the NIS2 directive, which introduces a profound change in the approach to risk management. The legislation, in fact, is no longer limited to requiring the adoption of security measures, but requires companies to continuously and verifiably demonstrate their Risk Management Skills. This means that security is no longer a set of specific activities, but a continuous process that involves:
- Structured cyber risk management
- The documentation of training and prevention activities
- The constant evaluation of the human factor
In this framework, corporate cybersecurity becomes a central element of corporate governance, with direct impacts on compliance, reputation and business continuity.
From awareness to the concrete implementation of security
Understanding the risk is the first step, but it is not enough: to truly reduce exposure, it is necessary to translate awareness into concrete and measurable actions. The starting point is the individual risk assessment, which makes it possible to analyze the level of exposure of each individual user and identify the most critical areas; this is accompanied by realistic attack simulations, essential for verifying the real behavior of people in the face of phishing and vishing attempts.
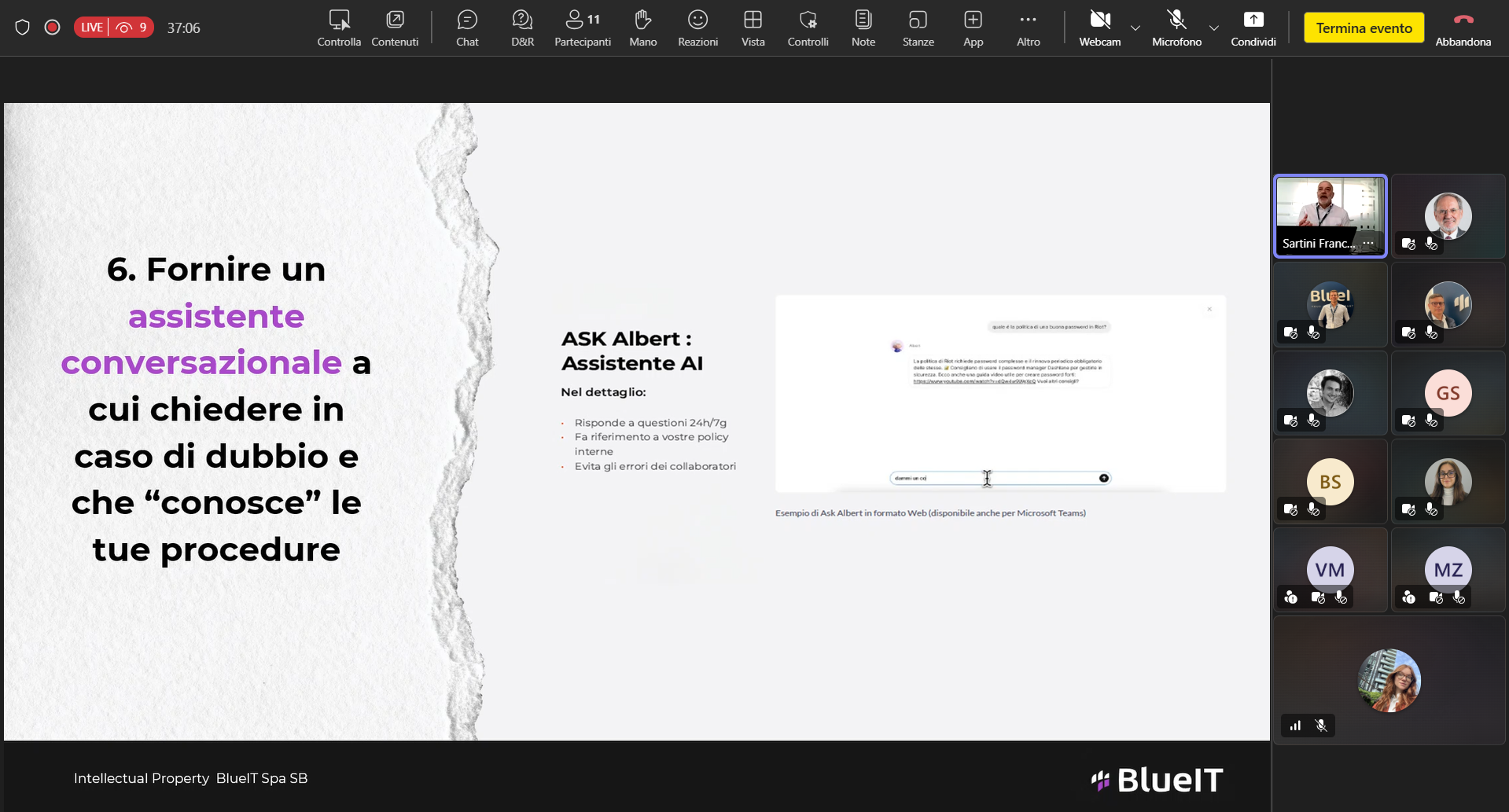
The translation of awareness into real security requires a continuous and integrated approach and Riot represents Blueit's technological answer: a platform that makes the corporate cybersecurity model based on people, processes and technology operational. Riot integrates training, simulations and cyber risk monitoring into a single environment, allowing organizations to continuously manage the human factor and automatically produce the evidence required by NIS2. Thanks to its scalable architecture and Data Sovereignty (EU), Riot allows companies to move from sporadic interventions to a constant, measurable and data-driven security model.

Cybersecurity as a strategic business lever
Corporate security is now a strategic lever and no longer just a technological one: the evolution of threats, the impact of artificial intelligence and the requirements of NIS2 make the role of the human factor central. Only an integrated approach between people, processes and technology makes it possible to build organizations that are truly resilient and capable of reacting to attacks. The real question is no longer how secure the infrastructure is, but how well the organization is able to recognize and manage a real attack.
Strengthen your business cybersecurity
We support companies in strengthening their corporate cybersecurity with an integrated approach and we help organizations to reduce cyber risk.
Contact us to deepen and request assessment, training and targeted simulation services: together we can transform the security of your business into a continuous and measurable process.
.png)
The most popular articles
Discover the latest news and trends


.png)
.png)
